How to Identify and Isolate Shared State Before Touching a COBOL Module
COBOL changes often break far beyond the module being edited because shared state hides in copybooks, WORKING-STORAGE, DB2 cursors, CICS containers, JCL datasets, and implicit system variables that create invisible cross-program dependencies.

A developer modifies a COBOL module that handles fee calculations for a batch billing cycle. The change is small: a revised rate table lookup. Unit tests pass. Integration tests against the module's own inputs and outputs pass. The developer promotes to production on Friday evening.
By Monday morning, three downstream batch jobs have produced corrupted output. Account statements show wrong balances. A reconciliation job abends with a data exception. A regulatory report contains duplicated rows. None of these jobs were touched.
The root cause takes four days to find. The fee module shares a COPY member with two other programs. That copybook defines a record layout for a VSAM intermediate file. The change shifted a field boundary, but only the fee module was recompiled. The downstream programs still expected the old layout. Every record they read was misaligned by four bytes.
This is not hypothetical. As IN-COM documents, mainframe environments contain thousands of interdependent programs, shared copybooks, embedded SQL, and JCL scripts with invisible dependencies. Before you touch any COBOL module, you need to map every form of shared state it participates in.
Why Shared State Is Harder to Find in COBOL Than in Modern Languages
In Java or Python, shared state is explicit. You declare a class field, pass an object reference, or open a database connection. The type system makes coupling visible.
COBOL has none of these guardrails. Four properties make its shared state uniquely hard to find.
No encapsulation by default. Every data item in WORKING-STORAGE is accessible to the entire PROCEDURE DIVISION. EXTERNAL items let programs share memory without parameter passing.
WORKING-STORAGE persists across calls. According to IBM's Enterprise COBOL documentation, WORKING-STORAGE items persist in their last-used state for the duration of the run unit. One call can set a flag that silently changes the behavior of a later call.
COPY members silently couple programs. A copybook defines a record layout once. Dozens of programs include it. Change the layout and recompile one program, and you create a binary incompatibility with every other program that was not recompiled.
Global system variables are read by everything. RETURN-CODE, SQLCODE, and SQLSTATE are set by one program and read by the next. No declaration is required. The coupling is entirely implicit.
The Seven Types of Shared State in COBOL
Every shared state problem in COBOL falls into one of seven categories. For each type: what it is, where it lives, how to detect it, what breaks if you miss it.
1. WORKING-STORAGE (Persistent in CICS)
The program's primary data area. It remembers values between calls. In batch, it persists for the run unit. In CICS, IBM states that CICS creates a separate copy per transaction, but the storage lasts while the program is running within that transaction.
Detect: Search for data items set in one CALL and read in a subsequent CALL without reinitialization. In threaded environments, IBM notes that simultaneous invocations share a single copy, creating race conditions. Fix: Use LOCAL-STORAGE, which allocates a fresh copy per call:
WORKING-STORAGE (persists across calls):
WORKING-STORAGE SECTION.
01 WS-CALL-COUNT PIC 9(4) VALUE 0.
PROCEDURE DIVISION.
ADD 1 TO WS-CALL-COUNT
- Second call sees 2. Value persists.
LOCAL-STORAGE (fresh copy per call):
LOCAL-STORAGE SECTION.
01 LS-CALL-COUNT PIC 9(4) VALUE 0.
PROCEDURE DIVISION.
ADD 1 TO LS-CALL-COUNT
- Always 1. Freed on RETURN.
2. EXTERNAL Data Items
Shared memory segments that any program in the run unit can read and write, without parameter passing. Declared with IS EXTERNAL in WORKING-STORAGE. The runtime allocates one shared copy. The GnuCOBOL documentation confirms that a definition mismatch raises a fatal EC-EXTERNAL-DATA-MISMATCH exception.
Detect: Grep all source for IS EXTERNAL. Cross-reference every program declaring the same item name. Verify declarations are byte-identical. Risk: Change the layout in one program without recompiling all others, and those programs read garbage.
- Both Program A and Program B declare this.
- The runtime allocates ONE shared copy.
WORKING-STORAGE SECTION.
01 SHARED-CONFIG IS EXTERNAL.
05 CFG-RATE-TABLE PIC X(8).
05 CFG-MAX-RETRY PIC 9(3).
05 CFG-TIMEOUT-SEC PIC 9(5).
3. Shared COPY Members (Copybooks)
Reusable source fragments included at compile time. They define record layouts for files, COMMAREA structures, and DCLGEN declarations. Any copybook referenced by more than one program is a coupling point.
Detect: Run a cross-reference report on your source library. IN-COM's SMART TS XL provides cross-reference, data lineage mapping, and control flow diagrams for this. Risk: Change a field size in a copybook and recompile only one program. Every other program has a binary mismatch. This is the exact failure from the opening scenario.
4. DB2 Open Cursors
A cursor is a pointer into a DB2 result set. When a program opens a cursor and calls another program, the cursor stays open. IBM's DB2 documentation specifies that a cursor remains open until an explicit CLOSE or the end of the unit of work.
Detect: Trace EXEC SQL DECLARE CURSOR, OPEN, FETCH, and CLOSE across all programs in the call chain. Look for cursors left open before a CALL. Risk: A called program issues COMMIT, closing all cursors not declared WITH HOLD. The caller tries to FETCH from a closed cursor: SQLCODE -501.
5. CICS Shared Containers and Channels
Channels are named envelopes holding containers (named data blocks), passed between programs on LINK, XCTL, or RETURN. Planet Mainframe notes containers have no size restriction and are visible only to participating programs. Older systems also use the Common Work Area (CWA) and TCTUA, accessible by any transaction in the CICS region (IBM CICS TS documentation).
Detect: Search for EXEC CICS PUT/GET CONTAINER and EXEC CICS ADDRESS CWA/TCTUA. Map writers and readers. Risk: A program changes container format. Downstream programs interpret data using the old layout. CWA corruption is worse: it affects every transaction in the region.
6. JCL DD Statement File References
DD statements map logical file names to physical datasets. When two job steps reference the same dataset, they share file state. Tripwire's analysis highlights that poorly secured batch jobs can expose shared datasets, and embedded credentials in JCL compound the risk.
Detect: Parse all JCL. Extract DD names and DSN values. Build a matrix of which steps read or write each dataset. Risk: Change the record layout in Step 1; Step 2 reads misaligned records with no JCL error.
//STEP01 EXEC PGM=FEECALC
//OUTFILE DD DSN=PROD.FEE.INTERMEDIATE,
// DISP=(NEW,CATLG,DELETE),
// SPACE=(CYL,(50,10)),
// DCB=(RECFM=FB,LRECL=200,BLKSIZE=0)
//*
//STEP02 EXEC PGM=BILLGEN
//INFILE DD DSN=PROD.FEE.INTERMEDIATE,
// DISP=SHR
//* STEP02 reads the file STEP01 wrote.
//* A layout change in FEECALC breaks BILLGEN.
7. Implicit System Variables
RETURN-CODE, SQLCODE, and SQLSTATE are special registers set by one program and read by the next. No declaration is needed. No import makes the dependency visible.
Detect: Search all programs for references to RETURN-CODE, SQLCODE, SQLSTATE. Map which programs set them and which read them. Risk: A program checks RETURN-CODE after a CALL, but the called program never sets it. The value is stale from a prior call. Branching decisions based on stale values produce intermittent failures that depend on call order.
Detection Tools and Methods
Static analysis. IBM's SCLM and tools like Micro Focus Enterprise Analyzer generate cross-reference reports mapping program-to-copybook, program-to-table, and program-to-file relationships. IN-COM's SMART TS XL reveals cross-program, cross-database, and cross-platform interactions visually.
Manual COPY member audit. Extract every COPY statement. Group by copybook name. Verify all programs were compiled against the same copybook version. Include PROC libraries in the scan.
JCL parsing. Build a dataset-to-step matrix from all JCL and cataloged procedures. This reveals file-level coupling invisible at the COBOL source level.
Runtime tracing. CICS auxiliary trace and DB2 trace capture actual interactions: LINK targets, cursor operations, container access. These catch dynamic behavior that static analysis misses.
AI tools. LLMs can parse COBOL source to identify COPY statements, EXTERNAL declarations, and EXEC SQL blocks. They cannot trace runtime state or determine whether a stale WORKING-STORAGE value actually affects a downstream program. Use them for the first pass. Do not rely on them for completeness.
The Isolation Playbook
Once you have mapped shared state, isolate it before modifying any module.
Migrate WORKING-STORAGE to LOCAL-STORAGE. For any variable that does not need to persist across calls, move it to LOCAL-STORAGE. This eliminates stale-value bugs. Test carefully: some programs intentionally rely on persistence. For a systematic approach to unit testing programs that share state, establish harnesses that exercise cross-call persistence scenarios.
Encapsulate shared copybooks. Do not modify a shared copybook directly. Create a new version. Update your program to use it. Add a translation layer between old and new layouts. Recompile dependents incrementally. This is the approach described in how the strangler fig pattern handles shared state during migration.
Add explicit RETURN-CODE checks. Before relying on RETURN-CODE after a CALL, add MOVE 0 TO RETURN-CODE before the CALL. This ensures you read a value set by the intended program, not a leftover.
Close cursors explicitly. Before calling another program, close open DB2 cursors. Document WITH HOLD cursors in the program comments and cross-reference matrix.
Replace CWA with containers. The CWA is accessible by every transaction in the CICS region. Replace it with named containers on explicit channels, limiting visibility to the call chain.
The Specific Risk of CICS WORKING-STORAGE Corruption
CICS storage corruption produces failures that look completely unrelated to the change that caused them.
Every CICS task storage allocation is flanked by a Storage Check Zone (SCZ): a small block of bytes containing a constant derived from the subpool ID and task number. It functions as a tripwire. IBM's CICS TS documentation states that CICS detects violations by checking these zones when the application issues a FREEMAIN, and when it releases all remaining user-task storage at task termination.
The critical detail: the violation is detected not when it occurs, but only when the SCZ is checked. A program can overwrite the trailing SCZ and continue executing. CICS notices only when the storage is freed, which may be in a different program entirely.
A developer changes a COBOL module and introduces a field that writes one byte past the end of a WORKING-STORAGE structure. The byte overwrites the trailing SCZ. The program returns. The calling program makes another EXEC CICS request. CICS checks the SCZ, detects corruption, issues an SM0102 abend, and takes a system dump. The dump points to the calling program, not the one that caused the overflow.
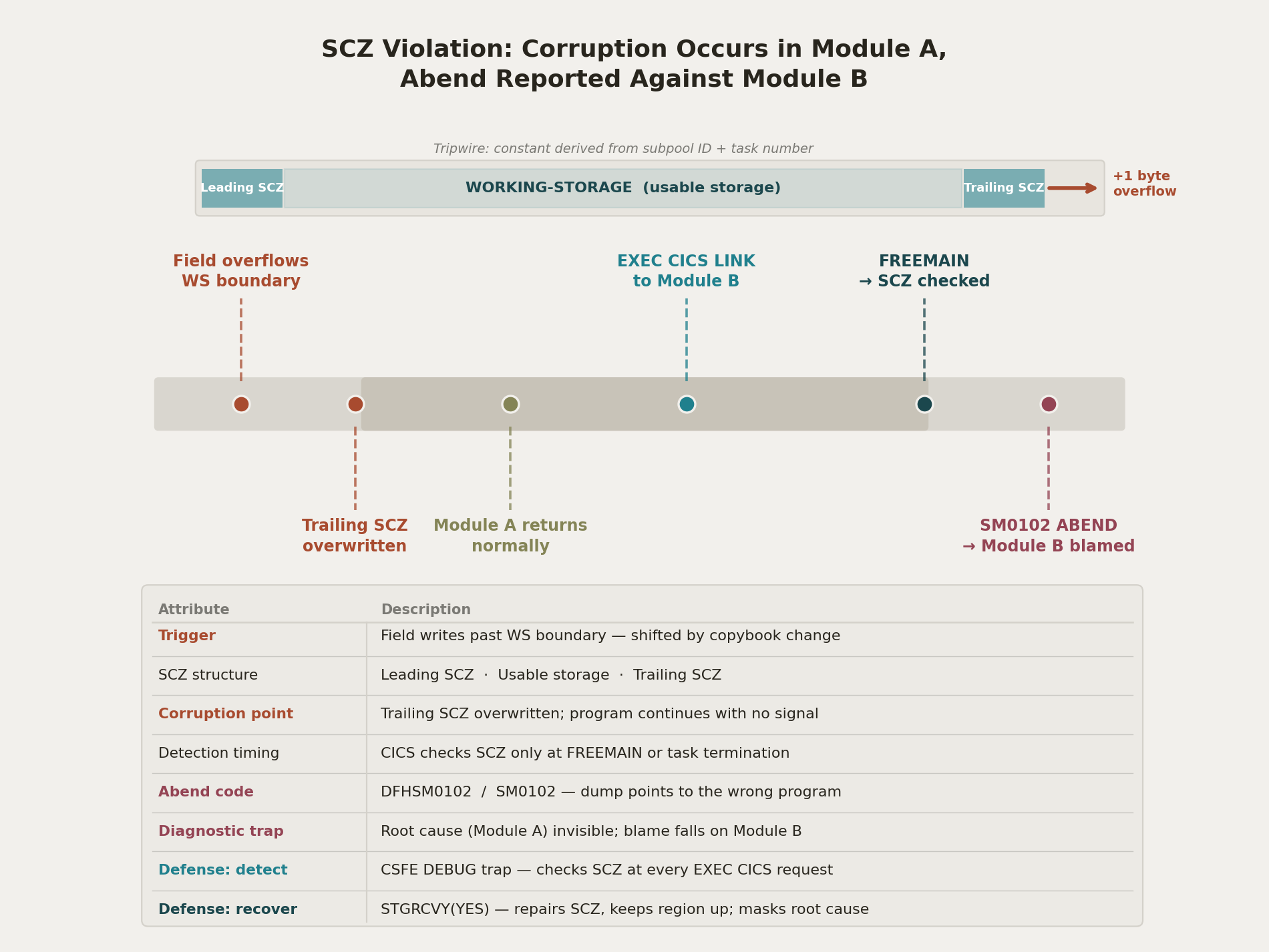
SCZ corruption: overflow in one module, abend in another.
The IBM Mainframe Forums document a real case where WORKING-STORAGE corruption caused a DFHSM0102 storage violation traced to an SCZ overwrite. If the leading SCZ is overlaid, IBM notes, an unrelated transaction may be responsible, because task storage elements may be contiguous in memory. At the enterprise level, the IBM z/OS Coupling Facility adds another dimension: shared structures across address spaces introduce storage constraints that compound the risk of cross-system state corruption.
Defense: run CICS with CSFE DEBUG Storage Violation Trap during testing. This checks SCZs at every EXEC CICS request, catching violations closer to the point of origin. In production, STGRCVY(YES) repairs corrupted SCZs but masks the root cause. Use it for resilience, not diagnosis. For how these risks compound during modernization, see the hidden risks article.
Static analysis finds roughly 80% of shared state in a COBOL codebase. The remaining 20% is dynamic: runtime-dependent cursor states, conditional CALL chains, CWA writes under error conditions. That 20% shows up in production.
The goal of isolation work is not zero breakage. It is blast radius reduction. If you migrate a variable to LOCAL-STORAGE, a stale-value bug is confined to one call. If you encapsulate a copybook behind an adapter, a layout change hits one translation layer instead of twenty programs. If you replace CWA with containers, corruption affects one call chain instead of every transaction in the region.
Map the state. Isolate it. Then make your change. The four days you spend on detection save the four weeks you would spend on a production incident.